Overview
This post documents the last major piece of installation for the System Center 2012 R2 Service Provider Foundation.
Other posts in this series are:
Prerequisites
Service Provider Foundation is a
component of System Center 2012 R2 Orchestrator. If you haven't already
unpacked this from the System Center 2012 R2 Preview download, run
"SC2012_R2_PREVIEW_SCO.exe" now to prepare the installation source.
Disable Internet Explorer Enhanced Security Configuration
Disable IE Enhanced Security Configuration using a script to from this Stack Overflow post.
This is required as the System Center 2012 R2 Orchestrator installer
displays the landing page an IE control, which will warn if enhanced
security is enabled.
function Disable-InternetExplorerESC
{
$AdminKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A7-37EF-4b3f-8CFC-4F3A74704073}"
$UserKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A8-37EF-4b3f-8CFC-4F3A74704073}"
Set-ItemProperty -Path $AdminKey -Name "IsInstalled" -Value 0
Set-ItemProperty -Path $UserKey -Name "IsInstalled" -Value 0
Stop-Process -Name Explorer
Write-Host "IE Enhanced Security Configuration (ESC) has been disabled." -ForegroundColor Green
}
function Enable-InternetExplorerESC
{
$AdminKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A7-37EF-4b3f-8CFC-4F3A74704073}"
$UserKey = "HKLM:\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A8-37EF-4b3f-8CFC-4F3A74704073}"
Set-ItemProperty -Path $AdminKey -Name "IsInstalled" -Value 1
Set-ItemProperty -Path $UserKey -Name "IsInstalled" -Value 1
Stop-Process -Name Explorer
Write-Host "IE Enhanced Security Configuration (ESC) has been enabled." -ForegroundColor Green
}
function Disable-UserAccessControl
{
Set-ItemProperty "HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" -Name "ConsentPromptBehaviorAdmin" -Value 00000000
Write-Host "User Access Control (UAC) has been disabled." -ForegroundColor Green
}
Disable-InternetExplorerESC
System Prerequisites
Service Provider Foundation has
some additional prerequisites above and beyond those we've already installed for Virtual
Machine Manager. These are listed in the Service Provider Foundation installer as
follows:
- Operating System - Windows Server 2012 R2
- IIS Version 7.5 or grater
- IIS Management Scripts and Tools role service
- IIS Security Basic Authentication
- IIS Security Windows Authentication
- IIS Application Development ASP.NET 4.5
-
WCF Data Services 5.0 for OData V3
- .Net Features 4.5 WCF Services HTTP Activation
-
ASP.NET MVC 4 RC
- Management OData IIS Extension
- Virtual Machine Manager 2012 R2 Administrator Console
We've already satisfied the first two and the last one, so we need to run some scripts to install the rest.
Add-WindowsFeature "Web-WebServer" -IncludeManagementTools
Add-WindowsFeature "Web-Scripting-Tools"
Add-WindowsFeature "Web-Basic-Auth"
Add-WindowsFeature "Web-Windows-Auth"
Add-WindowsFeature "Web-Asp-Net45"
Add-WindowsFeature "NET-WCF-HTTP-Activation45"
Add-WindowsFeature "ManagementOdata"
This will leave two components
remaining - "WCF Data Services 5.0 for OData V3" and "ASP.NET MVC 4 RC".
These can be downloaded from the links in the list above. It's not
clear how to script the WCF Data Services install, so we'll just do that
the old fashioned way for now, but MVC 4 can be installed using the
commands below.
md c:\logs
set downloads=\\nas1\downloads\Microsoft
"%downloads%\Desktop Software\ASP.NET MVC 4\AspNetMVC4Setup.exe" /quiet
Domain Objects
Run the following script to create some Active Directory user groups to manage security permissions for the Service Provider Foundation web services:
Add-WindowsFeature -Name "RSAT-AD-PowerShell"
New-ADGroup -Name "SPFAdminSiteUsers" -SamAccountName "SPFAdminSiteUsers" -GroupCategory "Security" -GroupScope "Global" -DisplayName "SPF Admin Site Users" -Path "CN=Users,DC=va,DC=local" -Description "Members of this group can access the SPF Admin Site"
New-ADGroup -Name "SPFProviderSiteUsers" -SamAccountName "SPFProviderSiteUsers" -GroupCategory "Security" -GroupScope "Global" -DisplayName "SPF Provider Site Users" -Path "CN=Users,DC=va,DC=local" -Description "Members of this group can access the SPF Provider Site"
New-ADGroup -Name "SPFVMMSiteUsers" -SamAccountName "SPFVMMSiteUsers" -GroupCategory "Security" -GroupScope "Global" -DisplayName "SPF VMM Site Users" -Path "CN=Users,DC=va,DC=local" -Description "Members of this group can access the SPF VMM Site"
New-ADGroup -Name "SPFUsageSiteUsers" -SamAccountName "SPFUsageSiteUsers" -GroupCategory "Security" -GroupScope "Global" -DisplayName "SPF Usage Site Users" -Path "CN=Users,DC=va,DC=local" -Description "Members of this group can access the SPF Usage Site"
Add-ADGroupMember -Identity "SPFAdminSiteUsers" -Members "Domain Admins"
Add-ADGroupMember -Identity "SPFProviderSiteUsers" -Members "Domain Admins"
Add-ADGroupMember -Identity "SPFVMMSiteUsers" -Members "Domain Admins"
Add-ADGroupMember -Identity "SPFUsageSiteUsers" -Members "Domain Admins"
Installing Service Provider Foundation
Navigate to the folder you unpacked SCO2012_R2_PREVIEW_SCO.exe into, and launch SetupOrchesrator.exe, then follow the installation wizard as per below:
On the next page for the "Admin web service", change the security groups to the "va\SPFAdminSiteUsers"
group we created earlier. Leave the application pool credentials to Network Service, although we'd specify individual domain groups and
users for these purposes in a full production environment.
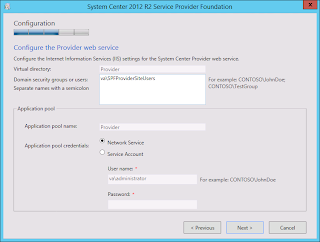
Do the same for the "Provider web service":
And the "VMM web service":
And finally, the "Usage web service":
This completes installation of the System Center 2012 R2 Service Provider Foundation. The final step in the next post will be to register the Service Provider Foundation endpoint with the Azure Pack mangement site.